This is utterly untrue.
It probably helps with better reading comprehension, 
Please refrain from slurs dannyf. I welcome if you have actual specific information about something I have misunderstood.
The "certain commands" deliberately harms reverse engineered chips,
To prove "harm", let alone "deliberately harm", you need intent.
To prove harm by someone, you need to prove a link between something someone did (or did not do in the case of neglect) and the harmful consequence for someone (or something). It may even be an accident. Though for deliberate harm we need something that shows intent (down to and including acts done in affect). FTDIs code proves something beyond that, as the preimage-attack shows premeditated intent.
...There are different types of harm like accidental harm-where the injury or damage is not caused by a...
How are you going to get that out of someone's head?
It is already out of their head. It is codified in the code. I follow the trail of evidence.
and does not only not do anything useful with FTDIs chips, it doesn't do anything at all with FTDIs chips.
Just how do you know that? It seems to me that unless you have intimate knowledge of the chip's design / functioning, you would have no way of knowing that.
It is understandable that you are trying to substantiate your points but it helps greatly if you do so on solid base.
I concur. This thread has been thorough but it is not given that any individual have seen the evidence of how we know it were on purpose. I should have referred to some of this evidence in the previous post. I'm sorry you had to request this information.
The FTDI FT232RL EEPROM is written 32 bits at once on the condition that a write to an odd address occurs, while a write to a even address is just buffered while it waits for a write to an odd address. This makes it possible for FTDI to attack the 16bits chips by writing to the even addresses and not follow up with a write to an odd address.
It is trivially easy to check that the writes doesn't update the FTDI produced chips. This means that it doesn't do anything at all with FTDIs chips. Just like I wrote.
It is doubly proved as it writes PID=0 to the chips, that would have bricked the FTDI produced chips as it would not be linked to the driver any more, nor would any windows version newer than XP work with it. Just like the attack against the reverse engineered chips now.
It is triply proved as the protocol analyzer shows that PID=0 is written to the chips, that would brick any FTDI chip, just like it does for the reversed engineered chips. If it were not for the fact that the FTDI driver writes just to the even addresses for the PID=0 sabotage - also proved by the protocol analyzer.
marcan proved that it is intentional and malicious, and disassembled the driver, and commented the code, and posted it for everybody to see and to verify, weeks ago, in this very thread:
In case anyone was still wondering if this is intentional and malicious...
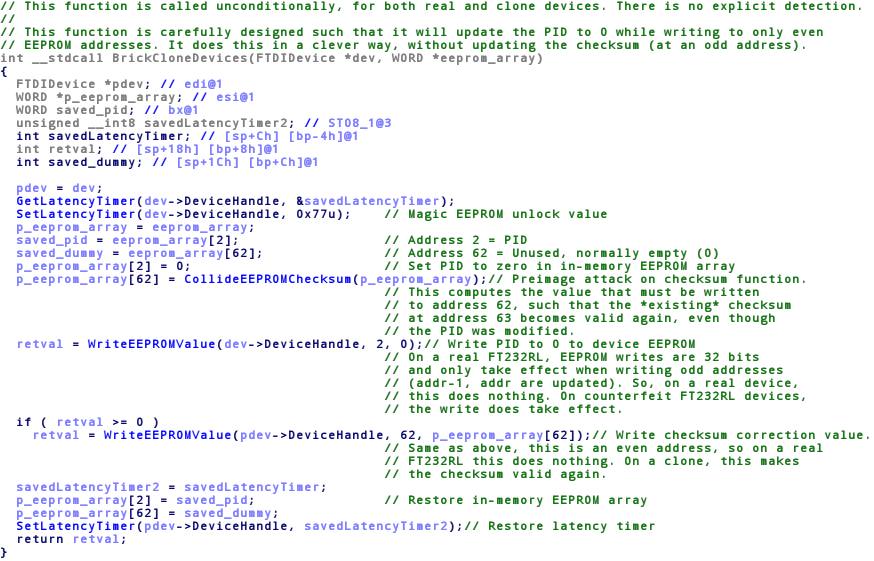
Straight out of their driver. Function/variable naming and comments mine.
I recommend that anyone that have any doubt of FTDIs intention read the actual code, and his post in full.
Before the actual attack, the FTDI driver does a preimage-attack on the checksum function as a preparation. This shows that it is a premeditated and willful act, not just a mistake.